Salam and hello to every one ...here's is the site you will find computer tips, tricks and hacking stuffs.. and much more... Have a good visit// Disclaimer: I'm not responsible for any damage done by the contents provided in this blog these are only for Educational Purpose..
Monday, December 27, 2010
How To Hack Victim,s Computer With Nmap And Metasploit
Today I am writing a tutorial on hacking with Nmap with Metasploit. First d/l Metasploit from the official website,Link:
Code:
http://www.metasploit.com/
Let all that install, and towards the end of the installation it will ask if you would like Nmap installed also,
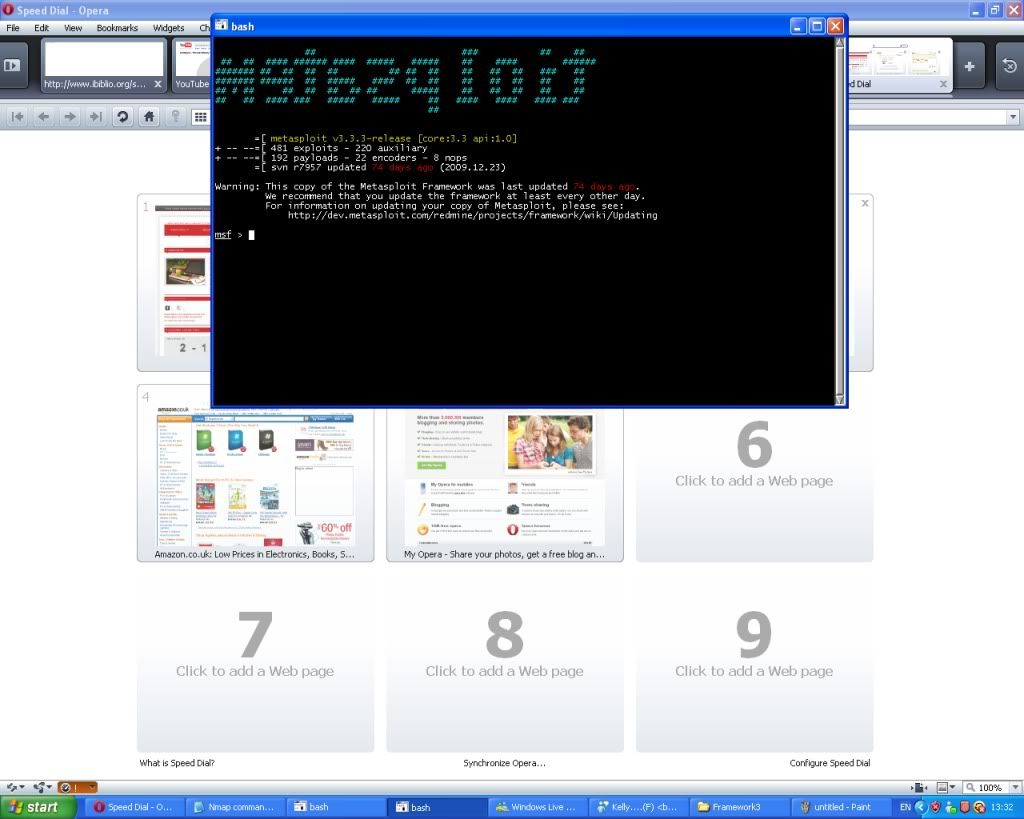
choose yes. Once you have that installed the Metasploit screen will open up as shown below...
Now type db_create
Once you have typed that type nmap
This loads nmap, as shown below....
You need to configure your scan now, I usually do a simple -sT -sV scan which will tell us the open ports and services running on the victims computer, Now type nmap -sT -sV xxx.xxx.xxx.x (X's being victims Ip number), Demonstrated below.
Now give it 5 minutes to complete the scan,Once that is complete if your lucky you should get a response like this...
This is basically a list of the open ports and services running on the target machine, Now the handy feature of the metasploit 3.3 framework is the autopwn feature, this basically searches and runs all matching exploits in the Metasploit database against the target machine and if successful will create a shell or similar privilege for the attacker.
Now once you have the nmap results delivered back to you showing the open ports and services type db_autopwn -p -t -e , From this point you will either have access to the victims computer through a successfully launched exploit or you will get a response saying the machine wasn't vulnerable to any of the exploits in the Metasploit database. Unfortunately on this particular machine I found it wasn't vulnerable as the image below proves.